A quick introduction to SL2™ Enterprise Capture
Overview
EMPOWERING COMPLIANT BYOD ACROSS +100 COUNTRIES
For BYOD customers, SL2 separates personal and work activity on the same smartphone. We deploy a separate, second phone number via the SL2 app. These are called Mobile Business Numbers™ (MBN) on employee phones to segregate work and personal communication. Voice and text/sms communication can be captured for review by compliance officers as well as archived for eDiscovery.
ONE PHONE, TWO OR MORE PHONE NUMBERS
We offer domestic and international numbers (MBN’s). We can text enable landline phone numbers. All communication passing through the SL2 platform can be archived via a partner for eDiscovery and long-term storage, as well as through simple solutions such as email journaling.
Secure Calls & Chat within Platform. Standard Voice SMS / MMS as well.
Supports FINRA, SEC, GLBA, SOX, DFA, IIROC, FCA, MiFID II, HIPAA, FOIA
Work
Compliance
Communications are time and date stamped, tracked, logged and archived for eDiscovery. A contextual history of user and customer communication via MBN is provided.
Separate Number (MBN)
BYOD deployments are assigned Mobile Business Numbers (MBN’s) on iOS and Android devices that separate work and personal calls, SMS and chat.
Safeguard assets
The organization controls the MBN assigned to devices. Subject to carrier requirements, if an employee leaves, the work number and associated contacts stay with the organization and can be transferred to another employee. Communications are eDiscoverable. Work data can be remotely wiped.

Personal
Personal Use
Information and apps on BYOD devices that are personal instead of business can remain untouched.
Employee Choice
Employees get to use their smartphone of choice with their preferred service plan.
Personal Privacy
SL2 does not use GPS or other features to identify, track, or reveal your location, so that this information is never captured or stored by SL2.
SL2 enables users to keep their personal messages separate: as long as you don’t send a personal message through SL2 or WhatsApp integrated with SL2, our system cannot access your personal messages.
Features
Multi-device support, multiple phone numbers, near real time desktop access and user management, SL2 ENTERPRISE CAPTURE DELIVERS.
User-Based, Multi-Device Access
Voice and messaging capabilities on registered smartphones, tablets and desktop—same Mobile Business Number™ (MBN).
Multiple MBNs
Assign multiple phone numbers (MBNs) to a single user.
Cellular/SIM or VoIP Calling
Make calls using VoIP, or use your Cellular/SIM carrier in bandwidth challenged environments.
Contacts and Calendar
Import thousands of contacts quickly and schedule messages to be sent at a later time.
Automatic Replies
Let customers know you’re not available. Refer someone else who can respond / help.
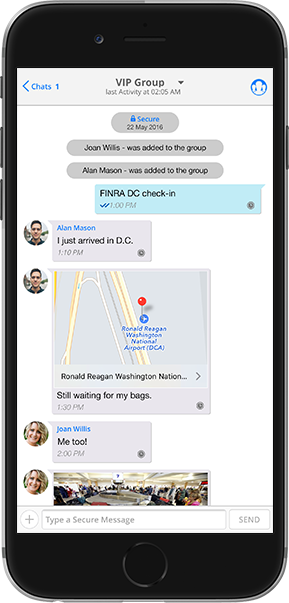
Groups / Organizational Units
Create group chats with unlimited people. Groups can be based on organizational units.
Email Journaling
SL2 provides app users an email summary of all messaging communications app-to-app and app-to-external contacts during the previous 24-hour period for easy recall.
Paging / Broadcast Messages
With pager messages, the device continues to notify until answered, like a traditional pager. Broadcast messages are one-to-many for announcements.
User-Based Policies & Compliance
Grant limited system access based on job function. Define distinct policy groups and push policies to users directly from the desktop portal.
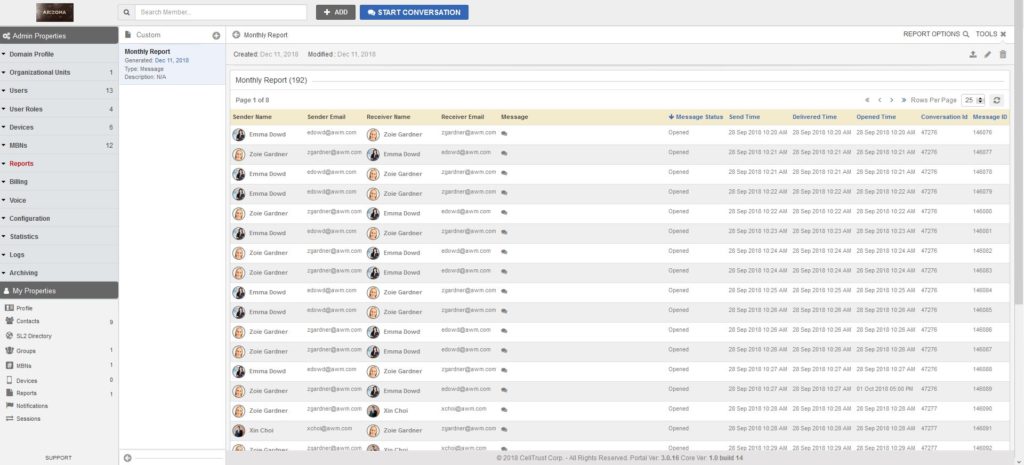
Dashboards & Reporting
Users can track message and voice activity. Compliance can filter and customized reports at the organization, group and user level.
SecureSMS® – Patented
Secure app-to-app communication with AES encryption in-transit and at-rest. Standard SMS / MMS as well.
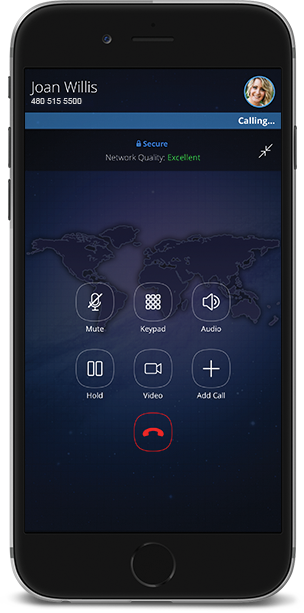
SecureVoice™ – Patented
Captures all calls made, metadata, can provide audio recordings. Voice app-to-app with AES encryption in-transit and at-rest. Standard voice calls. Works on Wi-Fi, data or SIM card.
Encrypted File Transfer / MMS
Send encrypted files and MMS and they are archived. The app encrypts the entire message library, and files are encrypted in transit, at-rest and on servers.
Reliability and Cost Saving when Roaming
Typically, Wi-Fi and data calls are more cost efficient when roaming.
Hosted in Microsoft® Azure
For ease of deployment, security, scalability and redundancy, SL2 is hosted in the Microsoft Azure cloud.
The following CellTrust patented technologies are used within SL2™ Enterprise capture:
Patent 11,451,660 System and method for tracking and archiving mobile communications
Patent 10,778,837 System and method for tracking and archiving mobile communications
Patent 10,992,802 System and method for tracking sms messages
Patent 10,412,215 System and method for tracking and archiving mobile communications
Patent 9,775,012 System and method for tracking SMS messages
Patent 9,686,660 Secure mobile information management system and method
Patent 9,572,033 Systems and methods for encrypted mobile voice communications
Patent 9,154,612 Secure mobile information management system and method
Patent 7,920,851 Secure mobile information management system and method
CA 2909613 System and method for tracking sms messages
EP 3 304 842 System and method for tracking and archiving mobile communications
EU 3304842 System and method for tracking sms messages
EU 2984863 System and method for tracking sms messages
HK1220855 System and Method for Tracking SMS Messages
Malaysia Patent No. MY-172205-A System And Method For Tracking SMS Messages
PH 1-2015-502384 System and method for tracking sms messages
SG 11201506971R System and method for tracking sms messages
SG 11201709823P System and method for tracking sms messages
Voice Calls

WORK AND PERSONAL VOICE CALLS ON A SINGLE DEVICE
Patented technology captures all incoming and outgoing calls made on a mobile device and provides audio recordings to help meet supervision and compliance needs. Now it is possible for businesses to issue their workforce with an Apple iOS™ based or Android™ based mobile phone, or allow employees to bring their own devices—and be in support of compliance.
SINGLE NUMBER REACH
Single or multiple MBN’s and many devices (phones, tables, desktop). Integrate your existing PBX and use your existing phone numbers.
Cellular/SIM or VoIP Calling
Make calls using VoIP, or use your Cellular/SIM carrier in bandwidth challenged environments.
SECURE VOICE
Powerful encryption and traceability for highly sensitive calls using WiFi, data or SIM on 3G, 4G and soon 5G networks. Reliability and cost savings while roaming.
DUAL PERSONA
Employees keep their personal phone and SMS private. Work communication is safeguarded, app-to-app communications encrypted, all via MBN’s.
COMPLIANCE
SL2 Enterprise Capture provides tools to help meet FINRA, SEC, GLBA, SOX, DFA, HIPAA, and FOIA in the United States; IIROC in Canada; FSA and FCA in the United Kingdom; and MiFID II in Europe, among others.
Messaging
TRACK, LOG & ARCHIVE TEXT MESSAGES
All text messages sent using the app are time and date stamped, tracked, logged and can be archived for eDiscovery.
Compliance
Generate reports and manage policies organization wide, in organizational units, or device-specific on the Admin portal or through your UEM.
Secure Messaging
Text messaging with AES encryption in-transit and at-rest protects sensitive information and intellectual property on all SL2 app-to-app communications.
Email Journaling
Email journaling option delivers app users an email summary of all messaging communications, app-to-app and app-to-external contacts, during the previous 24-hour period for easy recall.
Data / Message Retention
Define the duration of a sent message’s availability and storage on the receiving device.
Message Status
Know when a message has been delivered, opened and deleted.
Urgent Messaging
Ability to override the silent mode of a device for urgent messages.
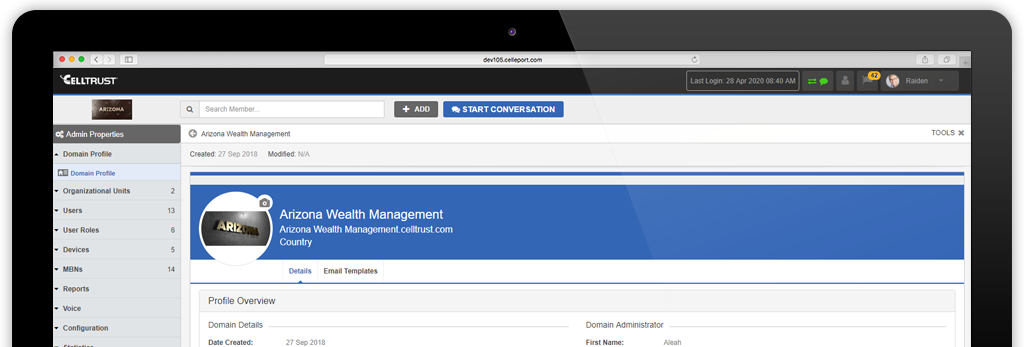
Desktop Access
SEAMLESS & SECURE FROM MOBILE TO DESKTOP
Access CellTrust SL2 via browser on any device for both messaging and calling in near real time. Since it is in near real time, you can use one device to send and another to respond simultaneously. Additional management features and benefits include:
- At-a-Glance Dashboard
- Address Book
- My Profile
- My Contacts
- My MBNs
- My Devices
- My Policies
- Report Center
MAXIMIZES LANDLINE ROI
Enable text messaging to your existing desk phone numbers

CLIENT CALL OR TEXT ONE PHONE NUMBER
After CellTrust enables your landlines for texting, the SL2 platform uses the caller ID of the landline. Clients only have one number to call or text and do not need SL2 on their phone.
SERVICE PROVIDER REMAINS THE SAME
Voice functionality of the landline and current service provider remains the same. Calls received on the landline number go to the desk phone and can be forwarded, or simultaneously ring, the user’s smartphone.
Compliance Control
COMPLIANCE TEAM HAS FULL CONTROL
SL2 Enterprise Capture’s administrative dashboard is an easy to use and configurable management platform. Configure archiving settings, assign Mobile Business Numbers, set and change rules and policies, and correlate and supervise voice, text, chat activities and more.
DASHBOARD WITH FULL OVERSIGHT AND REPORTING
Compliance teams maintain full oversight and control through the SL2 Enterprise Capture administrative dashboard. At a glance, supervisory staff have near real time oversight of user activity, organizational units, devices, policies, MBN’s, archiving, system logs and more across their network to monitor usage and ensure enterprise policies. With the SL2 Enterprise Capture reporting feature, compliance teams can filter and produce customized reports at the organization, group and user level on key data within their SL2 mobile communication network.
ON-BOARDING IS EASY
Once an MBN is provisioned by compliance or IT, the user can begin communicating immediately with all the integrated compliance and security features SL2 offers.
APPLY POLICIES TO WORK DATA ONLY
SL2 Enterprise Capture compliance controls only apply to work data via the MBN.
Archiving
SECURE REPORTING, AUDIT TRAILS & eDISCOVERY
To help mitigate risk and respond to eDiscovery and compliance demands, SL2 Enterprise Capture offers comprehensive reporting, audit trails, traceability and archiving integration. Also, all administrative and operator activities are logged for server audit trails, and intrusion attempts are logged for intrusion detection reports.
EASILY INTEGRATES WITH THE LEADING ARCHIVING TECHNOLOGIES

Choose from a custom archiving solution or one of CellTrust’s leading archiving technology partners to capture, manage and archive voice, chat, text and multimedia messages in support of eDiscovery and regulatory compliance.
Meet Regulatory Compliance & Evidentiary Standards: Including FINRA, SEC, IIROC, Dodd-Frank Act, GLBA, SOX, FCA, MiDFID II, FOIA, Sunshine Laws, HIPAA and other regulatory guidelines.
Searches: Quickly access metadata with built-in search tools.
Reporting: Leverage administrative access in order to audit content, receive intrusion reports and follow audit trails.
CHOOSE YOUR SL2 PLAN BELOW
Contact us for pricing
Number of Users up to 500
Options include:
Basic Authentication
SMS / MMS / GroupMMS
Private Calls
Contact Sync or import
Support
Email Journaling
Privacy Shield /GDPR
Contact us for pricing
Number of Users over 500
Everything in SMB, plus additional options:
EMM Integration
Security Key Management
Bring Your Own Key (BYOK)
File Type Restrictions
IP whitelisting
Emoji blocking
HSM
The above feature comparison does not reflect the entire SL2 feature set but rather is intended to serve as a guide to help our customers determine which product best meets their organizational requirements. Should you be interested in a particular feature not listed, don’t hesitate to contact us to discuss.

