Are You Prepared in the Case of a Data Breach?
I recently had the pleasure of representing the Association of Corporate Counsel by moderating a panel at the National Bar Association conference in Scottsdale, AZ. The panel, “Understanding Cybersecurity Risks: Issues & Trends,” included four exceptional speakers: Marcus A. Christian, Partner, Mayer Brown LLP; Lillian S. Hardy, Counsel, Hogan Lovells; Antonio D. Robinson, Vice President, Associate General Counsel, Carter’s Inc.; and Tori M. Silas, Privacy Officer & Senior Counsel, Cox Enterprises, Inc. My appreciation to Jim Merklinger, GC of ACC and Jennifer Chen, Director of the ACC Foundation, for providing this opportunity.

Panelist (from left to right): Marcus A. Christian, K Royal, Lillian S. Hardy, Tori M. Silas, Antonio D. Robinson
Photo credit: AJ Shorter Photography
We had a great deal of information to cover in one hour, and the session before us went 15 minutes over AND we were right before lunch. Needless to say, our panel was under a little pressure to manage our presentation in less than an hour. Nonetheless, the seasoned attorneys were unfazed and managed to not only wrap up on time, but left attendees with a better understanding and urgency to address cybersecurity risks.
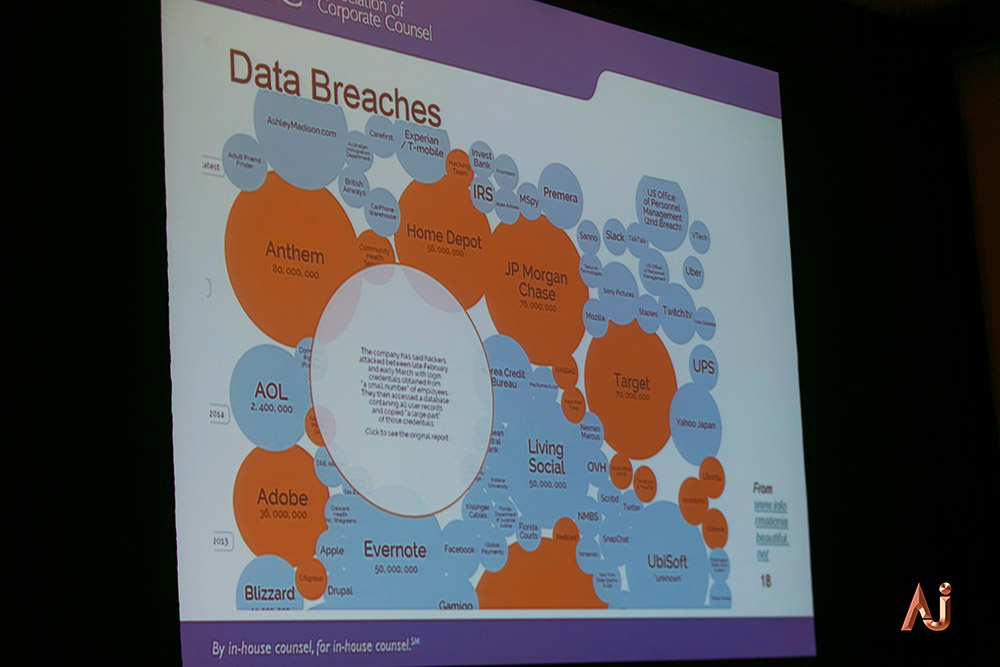
Marcus kicked off the panel discussion with a basic overview to understand cyber risk—the threats, impact, risk management, and current status of the cyber risk environment. Tori then walked us through a thorough yet very concise view of the U.S. regulatory framework. She gave some extra time to both recent enforcement action by the U.S. Federal Trade Commission and some insight to state laws and action. Tony followed with the structure of managing cyber risk—the framework. He discussed the International Standards Organization (ISO) and National Institute of Standards and Technology (NIST), among others. And as the last piece of the framework, Lillian covered data breaches, when our protected or confidential data is copied, transmitted, viewed stolen or used by an individual unauthorized to do so.
This set the stage as we presented a hypothetical breach to the audience:
- FBI discovers personally identifiable information (PII) of your company’s employees (including those in the UK) as well as 300,000 customers posted on Pastebin.
- The FBI formally notifies your company and requests an onsite visit to further discuss the apparent breach.
- On the same day, the corporate anonymous hotline receives allegations of an insider possibly facilitating a data breach that may be linked to the FBI notification.
Our panelists then walked through what should be done before a breach, during the breach, and post-breach, as well as a special review on communications. The most important takeaway given during this portion: make a breach response plan, test it, review it, and follow it—then repeat.
Implementation of an effective breach response plan allows organizations to fulfill their responsibilities to those individuals and entities that entrust the organization with PII. Following and maintaining a security breach response plan should also help businesses to comply promptly with legal requirements that apply to the organization, and to reduce the risk of a data security breach that causes serious harm to the company’s reputation and finances, especially due to of an inadequate response.
Again, my appreciation to the panelists. They truly were marvelous, especially given the time crunch. And my thanks to the Association of Corporate Counsel and the National Bar Association for providing this opportunity.