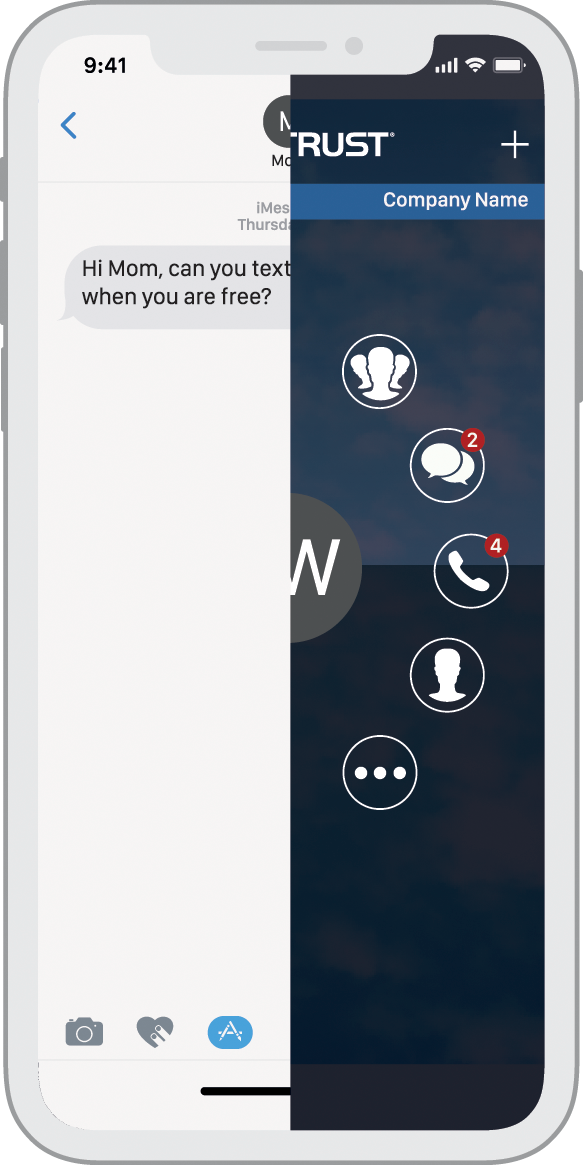
CellTrust SL2™ – Empowering Compliant BYOD
From employees to board members, a critical factor that will help drive lasting BYOD success is user experience. It is crucial as it impacts employee adoption, enables productivity and reinforces a positive mobile experience. Ultimately, usability and productivity matter, which is why we made the dramatic shift from device-centricity to user-centricity with CellTrust SL2™ to offer a flexible solution that works for the enterprise. From multi-device support, multiple MBNs, and extending account access and user management to the desktop—CellTrust SL2™ delivers the best of BYOD while helping organizations enhance mobile security in support of compliance.
UI / UX
Secure mobile communications has never looked so good. Our elegant design and user-centric functionality for iOS and Android delivers an enhanced mobile experience to foster enterprise adoption.
User-Based, Multi-Device Access
No longer tied to one device, users may access CellTrust SL2™ voice and messaging capabilities on registered smartphones, tablets and desktop—all using the same Mobile Business Number (MBN).
Multiple MBNs
Assign multiple MBNs to a single user, allowing professionals in healthcare, finance, insurance or other industries that work at multiple subsidiaries or regions, to have specific numbers tied to those groups.
File Transfer / MMS
Send encrypted file transfers and MMS with CellTrust SL2™ with the ability to archive. The app encrypts the entire message library, and files are encrypted in transit, at rest and on servers.

Groups / Broadcasts
Create group chats with unlimited people. Stay connected with internal and external contacts that you regularly communicate with and have the ability to broadcast important messages instantly.
Email Journaling
CellTrust SL2™ provides app users an email summary of all messaging communications app-to-app and app-to-external contacts during the previous 24-hour period for easy recall.

Desktop Client
From multiple devices to desktop—and even simultaneously—CellTrust SL2™ users can now manage and deliver their secure mobile communications where, when and how they choose.
Dashboards & Reporting
Users can easily track message activity, MBN minutes, registered devices and more, while IT administrators can filter and produce customized reports at the organization, group and user level.
User-Based Policies & Compliance
In addition to granting limited system access based on job function, IT administrators and compliance officers may now define distinct policy groups and push policies to users directly from the desktop client.